 Drew Angerer via Getty Images
Drew Angerer via Getty Images
Over the weekend, Google Project Zero researchers Tavis Ormandy and Natalie Silvanovich tweeted about discovering "the worst Windows remote code exec in recent memory." According to Ormandy, it could work against a default installation and even become "wormable" -- able to replicate itself on a targeted machine and then spread to other computers automatically. Now we know more about what the problem is since, in just two days, Microsoft's Security Response Center and Windows Defender developers were able to come up with a fix that is now available via Windows Update for Windows 7, 8.1, RT and 10, as well as other versions that IT professionals may be more familiar with.
As described by the Project Zero team, the problem resided in Microsoft's antimalware protection engine, which is supposed to scan files for issues, but could be tricked into executing code included in an email, on a webpage or in an instant message. Now that it's patched, your Windows computer should download the updated version automatically within the next day or two.
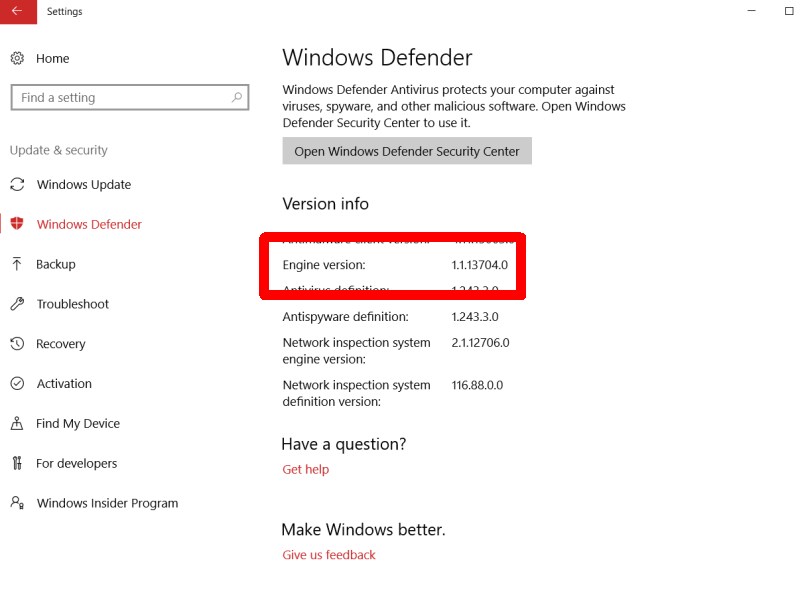
If you're in a hurry, you can punch the update button and get it manually, likely without a reboot -- just check your Windows Defender settings to make sure it has an engine listed with version 1.1.13704.0 or higher.
Just released malware protection engine update to
— Security Response (@msftsecresponse) May 9, 2017
address RCE vuln – Defender will autoupdate. https://t.co/rzn5QWo6sV
.@natashenka Attack works against a default install, don't need to be on the same LAN, and it's wormable.